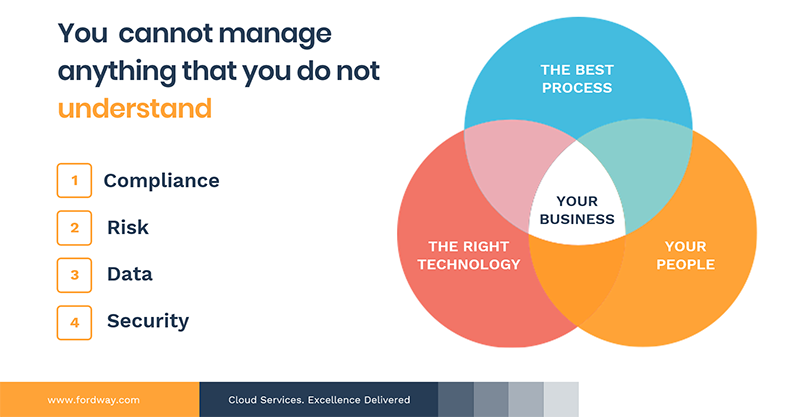
You want to innovate. To transform your organisation with new services and help achieve the top-line. Security and compliance can seem like endless red tape and bureaucracy that simply get in the way.
We know that in the age of digital transformation security is an issue for many organisations and so we recently ran an event in London to discuss the issues and suggest strategies that enable secure and innovative solutions. Done properly, compliance can create added value by opening up new markets and increasing revenue.
- Security and Compliance are a business issue. IT may implement security policy, but the organisation needs to set policy and define the organisation’s risk appetite. If you work in the IT team and find yourself trying to dictate policies you cannot do this in isolation. At the very least you need a Board Level Sponsor to help frame a business appropriate strategy and measures.
- The cost benefit of compliance versus the cost and risk of non-compliance need to be visible. Consistency and standardisation allow you to deliver quickly and with confidence by removing ambiguity. They speed up supplier selection because you have agreed criteria that must be met throughout your supply chain. What would the financial and reputational cost to your organisation be if you lost customer confidence? Consider reviewing your compliance and security requirements to see if you can implement further standardisation to deliver maximum business benefit and achieve new accreditation that supports your business strategy and builds trust. Dealing with compliance in a more ‘holistic’ way means that you will minimise cost and disruption to the organisation and you can then more easily tailor your IT infrastructure and systems to support your compliance needs.
- Secure services need to be designed for security from inception and tested (continuously). Many of the major breaches of 2018 were as a result of security simply being overlooked, which seems ridiculous when arguably we are more security aware than ever. In some cases these were web services where developers didn’t understand the implications of the way their application had been designed. In other cases – deemed ‘oops’ moments on the Information is Beautiful website – data was left completely unsecured. The best way to help avoid these issues is to design for security and privacy from the outset, train your staff to be aware of the issues, security test applications rigorously and test again every time you update your service, with the occasional spot test for auditing purposes.
- Log Everything! You do need to log everything. The average time to detect a breach is currently 196 days. How do you know what was lost or effective if you can’t review your logs? In the case of the Marriott Hotel breach reported in 2018, attackers had accessed the system for four years prior to detection. Advanced threat protection tools and security monitoring can help your organisation detect and mitigate breaches earlier. If you have log data, then you can review systems for malicious activity and get a true sense of the issue you’re handling. Remember that if you’ve detected a breach you must report it to the ICO within 72 hours, so it pays to be prepared and know how to respond!
- Choosing the right IT security solution for your business depends upon your risk appetite and strategy, so establish these and consider your supply chain before purchasing and implementing expensive solutions. In a supply chain situation, you are only as strong as your weakest link. If you are serving customers that expect a high standard of security you had better make sure that you are able to meet their expectations and be able to provide evidence through Cyber Essentials Plus, ISO 27001 and other key industry specific compliance requirements.
If you do them properly, security and compliance will reassure your customers that your systems and values are visible, secure and viable, supporting sales and driving revenue. They can also help increase revenue by giving you competitive advantage over your rivals and opening up new and potentially lucrative markets. So they deserve your time and attention.
If this is an area that you need assistance with why not arrange to talk to one of our experts?


